
Features 14.04.2026
AI Autopsy: Two iOS Kits Herald a New Era of Mass Exploitation
The era of permissive BYOD policies may be coming to an end

Features 14.04.2026
The era of permissive BYOD policies may be coming to an end
Remember when the Saudi Crown Prince hacked Jeff Bezos’ phone? At first glance, the incident might have led you to assume that mobile spyware is generally reserved for snooping on the elite. If that was ever the case, it’s certainly not anymore.
Two new developments have made it clear that phone-hacking kits first developed for intelligence agencies are now being targeted at the rest of us. This may have major implications for CISOs’ mobile security strategies.
On March 3, Google Threat Intelligence Group and iVerify both published research on Coruna, an iOS exploit kit that iVerify described as the world’s first mass iOS attack. Two weeks later, DarkSword arrived, another iOS exploit kit that iVerify found whilst researching Coruna. They both infected phones using nothing more than a visit to the wrong URL, and targeted people in large numbers.
“People in the space have been expecting an EternalBlue moment in mobile for a while” Rocky Cole
Trenchant, the surveillance arm of US government contractor L3Harris, is believed to have developed Coruna. Google first saw it being used by “a customer of a surveillance vendor”. But it didn’t stop there. It subsequently turned up on phones in Ukraine, and then things took a stranger turn.
“It leaked out of Trenchant, and it made its way to a secondary market: a zero-day broker,” says Rocky Cole, founder of iVerify. “That zero-day broker sold it to probably the Russian government and criminal groups in China, who bolted on their own modules and so stole cryptocurrency and PII with it.”
Former Trenchant general manager, Peter Williams, was recently sentenced to 87 months in prison for selling exploits to a Russian broker.
The repurposing of Coruna is enabled by a modular architecture that allows people to swap in new payloads. The crypto module hooks into 18 different crypto apps to exfiltrate wallet credentials. Today it steals digital currency, but the modular infrastructure stands ready for new instructions targeting corporate secrets, cloud credentials, or VPN tokens.
The path from targeted surveillance with mobile exploit kits to common deployment was a long time coming, says Cole. It’s been nearly 10 years since the same thing happened with EternalBlue. That vulnerability leaked from Cole’s former employer, the NSA, in 2017. Others turned it into a Windows exploit and used it to launch WannaCry and NotPetya, two show-stopping worms that mass infected the world.
“People in the space have been expecting an EternalBlue moment in mobile for a while,” Cole tells Assured Intelligence. “There are many of these exploit frameworks out there, and it was just a matter of time until they spun out of control.”
Coruna isn’t subtle. It uses five exploit chains targeting 23 vulnerabilities across iOS 13 to 17.2.1. Cole describes it as the ‘Lamborghini’ of mobile malware. First spotted by researchers circulating among threat actors in February 2025, the kit weaponises WebKit flaws CVE-2023-43000 and CVE-2024-23222, which are triggered when victims browse compromised legitimate sites.
The kit fingerprints devices first, matching iOS versions to exploit payloads. This surgical precision maximises success rates.
DarkSword affects devices running iOS 18.4 to 18.6.2. Like Coruna, it uses zero-days to infiltrate iOS, and like Coruna’s, they’re all patched now. However, the malware, which was written entirely in JavaScript, takes a fundamentally different approach by living off the land (LOTL) and abusing Apple’s own tools.
“Simply visiting a page can be enough to trigger exploitation” Kern Smith
Coruna has what Cole calls a “large blast radius”, but the fileless DarkSword malware doesn’t even get ring-zero access to the kernel (i.e. the most privileged access). Instead, it intercepts communications in the phone, slurping data including Wi-Fi passwords, text messages, call history, root location history, browser history, SIM card and cellular data. It also harvests health, notes, and calendar databases.
That’s a powerful tool to use against a population in conflict, which is exactly where iVerify found it. Its researchers spotted it on a suspicious URL that they found during the Coruna investigation, and saw that it was widely deployed in Ukraine. The attackers had also managed to infect a Ukrainian government domain, meaning anyone who visited it with a vulnerable phone got infected.
DarkSword is likely from a different source than Coruna, says iVerify, noting that it has Russian artefacts in the code. It comprises six vulnerabilities across two exploit chains, which were patched in stages, ending with iOS 26.3.
For CISOs, there are several takeaways. Simple cyber awareness won’t cut it. Training users not to click on suspicious links that could trigger these two exploit kits is standard operating procedure. And while we shouldn’t stop beating that drum, it isn’t enough.
“The use of hidden iFrames on compromised websites highlights how mobile attacks increasingly rely on passive delivery methods,” Zimperium VP of global solutions engineering, Kern Smith, tells Assured Intelligence. “Simply visiting a page can be enough to trigger exploitation, which means security strategies can’t rely on user awareness alone.”
Watering hole attacks don’t always use suspicious links. When perpetrators inject malicious iFrames into legitimate government websites, all bets are off. So technology has to play a part too. Mobile device management (MDM) will help to keep all corporate iPhones patched, neutralising these two exploit kits.
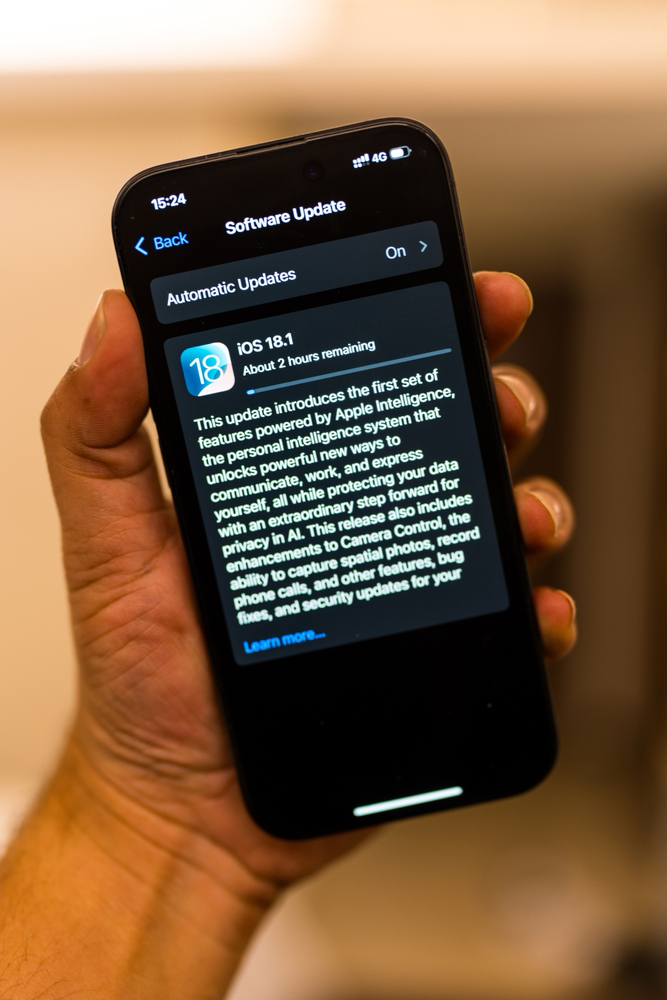
“In this case, you set up the auto update, and you push that and enforce it across all devices,” says Gareth Haken, director of cyber risk and resilience at the Information Security Forum (ISF). “So, in this scenario, that would solve the problem.”
“By allowing BYOD you are building in risk almost by default” Alex Jordan
Apple originally patched CVE-2023-43010 on iOS 17.2 in December 2023, but this month backported it through iOS 15.8.7. CISA also scrambled to add three Coruna vulnerabilities to its must-patch list while federal agencies raced to comply.
MDM could also allow automatic deployment of Apple’s Lockdown Mode. Designed for highly vulnerable (or high-value) users, it provides extra security protections at the cost of some convenience. Coruna ignores phones that have it enabled. However, as Cole points out, there are probably other kits running unnoticed. And MDM, designed for administration and configuration, isn’t designed to spot them.
DarkSword’s LOTL strategy makes detection especially hard for security tools. It leaves minimal forensic traces; mostly just standard Apple binaries doing what they’re designed to do. Security tools look for exploits and malware, not legitimate Apple binaries.
So the era of BYOD handsets might be over. The CISOs who let anyone’s phone connect to their network are at the greatest risk. “The default approach is to allow BYOD,” points out Haken’s colleague Alex Jordan, director of applications and tools at the ISF. “With those sorts of decisions that are taken by slightly smaller corporate players, you are building in risk almost by default.”
However, not all organisations will have the power to disallow BYOD devices. And many users will be unlikely to tolerate Lockdown Mode with its device constraints, warns Zimperium’s Smith.
“Lockdown Mode is a valuable control for individuals facing elevated risk, but it introduces usability trade-offs that make broad deployment difficult,” he says. “For most organisations, layered mobile security capable of detecting exploitation activity is the more scalable approach.”
But what layers? If MDM alone won’t cut it, what additional measures should companies take? “Organisations need visibility into compromise on the device itself, not just reliance on patching or traditional device management,” says Smith. So a layer of endpoint detection and response (EDR) is becoming table stakes for effective mobile device protection.
Secondary markets mean that the economics favour attackers, warns Cole. What cost millions to develop now sells for far less on criminal forums. Developing iOS exploits once required nation-state resources. Now criminal groups buy proven exploit chains, bolt on monetisation modules, and deploy at scale.
“What I hear is that at any point in time, there are a half dozen to a dozen of these kinds of things in circulation on the secondary market,” Cole concludes. So now, every organisation faces nation-state-grade attacks, regardless of their threat model.